合格させるVMware 1V0-81.20テスト問題でテストエンジンとPDFを提供中
あなたをお手軽に1V0-81.20試験合格させるリアル1V0-81.20練習問題集で更新されたのは2022年05月27日
質問 33
What is a unique benefit of Next Generation Antivirus over standard Antivirus?
- A. reactive analytics
- B. predictive analytics
- C. signature based heuristics
- D. file based heuristics
正解: B
質問 34
Which three are industry best practices of Zero Trust framework? (Choose three.)
- A. Employee machines need to have a passcode profile setup
- B. Employee machines on Internal network are trusted and have access to all internal resources
- C. Employees get access to only the required resources to get their job done
- D. Employee machines are checked for compliance before they get access to applications
- E. Employees are not required to provide MFA to access internal resources over VPN
正解: A,C,D
質問 35
Which VMware Carbon Black Cloud function allows an administrator to remotely run commands on protected endpoints?
- A. Live Query
- B. Alert Triage
- C. Investigate
- D. Live Response
正解: A
質問 36
In Workspace ONE Intelligence, which of the following is a role that can be assigned to an administrator account?
- A. Super User
- B. Automater
- C. Read-only
- D. Helpdesk
正解: A
質問 37
What is the safe course of action for a USB disk of unknown ownership and origin?
- A. Do not connect the USB to any computer as it may be a USB Killer device
- B. Connect the USB to a non-Windows device and examine it
- C. Connect the USB to an air gapped system and examine it
- D. Connect the USB device to your computer and allow the DLP software to protect it
正解: C
質問 38
Micro segmentation is under which pillar of trust in VMware's 5 pillars of Zero Trust?
- A. Session/Transport
- B. Application
- C. User
- D. Device
正解: A
質問 39
In a Workspace ONE deployment, Per App Tunnel uses the Native Platform API for which platforms?
- A. iOS & MacOS only
- B. Android & Windows only
- C. iOS & Android only
- D. iOS, Android, MacOS & Windows
正解: C
質問 40
In Workspace ONE Intelligence, which two are default components of the security risk dashboard? (Choose two.)
- A. Desktop Apps
- B. OS Updates
- C. Compromised Devices
- D. Web Apps
- E. Threats Summary
正解: C,E
質問 41
In VMware Carbon Black Cloud, what is the search field you would use when searching for a command line?
- A. command_line:
- B. process_commandline:
- C. full_cmdline:
- D. process_cmdline:
正解: B
質問 42
What is the default user's network range when creating a new access policy rule in Workspace ONE Access?
- A. 192.168.0.0/16
- B. LOCAL SUBNET
- C. 10.0.0.0/8
- D. ALL RANGES
正解: D
質問 43
Which three default connectors are available in Workspace ONE Intelligence to execute automation actions? (Choose three.)
- A. Workspace ONE UEM
- B. Slack
- C. vRealize Operations Manager
- D. Log Insight
- E. ServiceNow
正解: A,B,E
質問 44
Which shell command line syntax represents less suspicious danger than the others?
- A. -Enc
- B. sc create
- C. net user
- D. clear
正解: D
質問 45
Drag and drop the Cyber Kill events on the left into their proper sequential order on the right.
正解:
解説: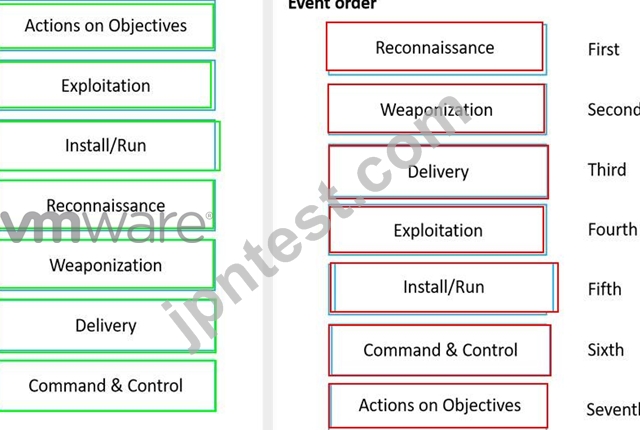
質問 46
An organization using VMware Carbon Black makes use of an unsigned third party application that is critical to business function. Unfortunately, the application has a reputation of Potentially Unwanted Program and is prevented from running based on the policy.
What Approved list mechanism will allow this application to run in your environment while maintaining the most secure posture?
- A. SHA-256 Hash based
- B. MD5 Hash based
- C. IT Tools based
- D. Certs based
正解: A
質問 47
Which parameter ensures an endpoint will stay connected with the designated VMware Carbon Black Cloud tenant?
- A. Company Code
- B. User ID
- C. Device Serial Number
- D. Organization Group ID
正解: B
質問 48
When you share a report in Workspace One Intelligence with a specified user, how is the report shared?
- A. Desktop Notification
- B. Console Message
- C. Email
- D. SMS
正解: C
質問 49
VMware's Intrinsic Security layer includes functionality for which control points?
- A. networks, containers, devices, users, and VMware Cloud
- B. networks, workloads, endpoints, identity, and clouds
- C. applications, workloads, devices, identity, virtual infrastructure
- D. applications, users, networks, data center perimeter, vSphere
正解: B
質問 50
In VMware Carbon Black Cloud Endpoint Standard, which items are available in the Event view?
- A. Connection, IP/Port
- B. Emails, Policies, OS, Locations
- C. IDs, Indicators/TTPs
- D. Hashes, Reputations
正解: A
質問 51
Refer to the exhibit.
Which statement is true about the firewall rule?
- A. It is a gateway firewall applied to a Tier-0 gateway that rejects traffic on port 22
- B. It is a distributed firewall applied to App-Services, DB-Servers and Web-Servers that drops traffic on port 22
- C. It is a gateway firewall applied to a Tier-0 gateway that drops traffic on port 22
- D. It is a distributed firewall applied to App-Services, DB-Servers and Web-Servers that rejects traffic on port 22
正解: C
質問 52
Refer to the exhibit.
From the VMware Carbon Black Cloud console, what page do you go to after clicking the Non-Malware bar in the Potentially Suspicious Activity chart?
- A. Alerts page with the selected alert filtered
- B. Investigate page with the selected reputation filtered
- C. Reputations page with the selected reputation filtered
- D. Notifications page with the selected alert filtered
正解: A
質問 53
Which VMware application enrolls an endpoint into Workspace ONE?
- A. Workspace ONE Intelligent Hub
- B. CB Defense Sensor
- C. VMware Horizon Client
- D. Workspace ONE Web
正解: A
質問 54
......
VMware 1V0-81.20 認定試験の出題範囲:
| トピック | 出題範囲 |
|---|---|
| トピック 1 |
|
| トピック 2 |
|
| トピック 3 |
|
| トピック 4 |
|
| トピック 5 |
|
| トピック 6 |
|
| トピック 7 |
|
| トピック 8 |
|
| トピック 9 |
|
| トピック 10 |
|
| トピック 11 |
|
| トピック 12 |
|
| トピック 13 |
|
1V0-81.20リアル無料試験問題と解答:https://www.jpntest.com/shiken/1V0-81.20-mondaishu
