あなたのCBSP試験100%合格問題集はここJPNTestで一発合格
突破上級者がシミュレーションされたCBSP試験問題集PDF
Blockchain CBSP 認定試験の出題範囲:
| トピック | 出題範囲 |
|---|---|
| トピック 1 |
|
| トピック 2 |
|
| トピック 3 |
|
質問 41
What is the easiest way to steal cryptocurrency from a user?
- A. None of the above
- B. Private key theft
- C. Eclipse attack
- D. Double-spend attack
正解: B
質問 42
Implementing data access as a blockchain smart contract is a good solution for generating an audit log of access to sensitive data
- A. False
- B. True
正解: B
質問 43
Which of the following is NOT a common regulatory requirement tor businesses?
- A. Data transparency
- B. Data encryption
- C. Data control
- D. Personal data protection
正解: A
質問 44
Stealth addresses are designed to do which of the following?
- A. Conceal transaction sender
- B. Conceal transaction amount
- C. Conceal transaction recipient
- D. Conceal shared secret
正解: C
質問 45
From a regulatory perspective, which of the following may be the most complicated issue around demonstrating proper data management?
- A. Use of distributed storage
- B. Lack of access controls
- C. Lack of blockchain support for encryption
- D. Decentralized control of blockchain
正解: A
質問 46
Both sidechains and slate channels rely on the original blockchain for security and as a fallback if issues occur.
- A. True
- B. False
正解: B
質問 47
Ring signatures are designed to do which of the following?
- A. Conceal transaction sender
- B. Conceal transaction amount
- C. Conceal shared secret
- D. Conceal transaction recipient
正解: A
質問 48
Which smart contract auditing strategy identities which variables in the function can be affected by the person running it?
- A. Control Flow Analysis
- B. Manual Code Analysis
- C. Symbolic Execution
- D. Taint Analysis
正解: C
質問 49
Malware infections of blockchain nodes can compromise the security of the blockchain's consensus algorithm.
- A. False
- B. True
正解: B
質問 50
This sample code is vulnerable to which of the following attacks? Select all that apply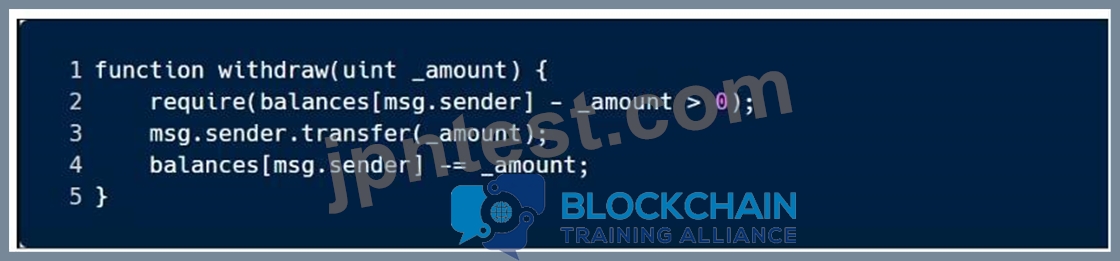
- A. Arithmetic
- B. Unchecked Return Values
- C. Short Addresses
- D. Race Conditions
正解: A
質問 51
Which blockchain security control either risks centralization or permanently divergent chains?
- A. Private Blockchains
- B. Permissioned Blockchains
- C. Random Neighbor Selection
- D. Checkpoints
正解: A
質問 52
Which of the following are common inputs to the algorithm to select the next block creator in Proof of Stake?
Select all that apply
- A. Stake Size
- B. Age of User Account
- C. User Activity on the Blockchain
- D. Time Since Last Chosen to Create a Block
正解: A,C,D
質問 53
Which of the following are good ways to get pseudo-random numbers for smart contracts?
- A. Private functions
- B. Block hashes
- C. Private variables
- D. External oracle
正解: D
質問 54
Which of the following is NOT an essential part of Confidential Transactions?
- A. Pederson Commitment
- B. Zero-Knowledge Proof
- C. Ring Signature
- D. Elliptic Curve Cryptography
正解: B
質問 55
Which of the following blockchain consensus algorithms is the most sustainable long-term?
- A. Proof of Burn
- B. Proof of Space
- C. Proof of Stake
- D. Proof of Work
正解: C
質問 56
Confidential Transactions prove that inputs and outputs ot a transaction are equal.
- A. False
- B. True
正解: B
質問 57
Properly encrypted data stored in the distributed ledger adequately protects data in both the short-term and the long-term
- A. False
- B. True
正解: B
質問 58
Quantum computers threaten traditional cryptography because they provide polynomial solutions to mathematically "hard" problems
- A. False
- B. True
正解: B
質問 59
Determining if a transaction is part of the distributed ledger is less computationally intensive in DAG-based solutions than in blockchain
- A. False
- B. True
正解: B
質問 60
Checkpointing is designed to protect against an attacker exploiting the mechanism by which blockchain resolves divergent chains
- A. False
- B. True
正解: B
質問 61
......
CBSP問題集トレーニングコース完全版:https://www.jpntest.com/shiken/CBSP-mondaishu
